The web, increasing transportation, and globalization have created a extremely interconnected provide chain. Your meals and garments are produced in numerous international locations, hopping from place to position till they find yourself at a neighborhood retailer. Whereas merchandise are extra accessible than ever, this interconnectedness additionally means extra dangers.
Disruptions will be something from shock climate to malicious cyberattacks. With so many new publicity variables, companies have to suppose past primary logistics. They want proactive, strategic plans to handle dangers. Provide chain threat administration (SCRM) helps your group predict dangers and preserve operations for higher long-term efficiency. A risk-based method lets firms construct stronger, extra aggressive provide chains in an more and more unpredictable world.
What Is SCRM?
Provide chain threat administration is figuring out, assessing, dealing with, and monitoring hazards that may affect your provide chain. Disruptions would possibly affect uncooked materials sourcing, transportation, cybersecurity, and some other a part of the availability chain threat administration course of. The purpose is to create a plan to reduce dangers affecting your online business.
An efficient SCRM program considers inner and exterior dangers. When you aren’t ready, operational inefficiencies can sluggish an operation down as a lot as geopolitical shifts. Since provide chains are fabricated from a number of tiers of suppliers, companions, and techniques, disruptions wherever alongside the chain can have a ripple impact on manufacturing and supply. As a substitute of ready to right after these disruptions, SCRM helps companies perceive their vulnerabilities and plan to keep away from slowdowns proactively.
Kinds of Provide Chain Dangers

A robust provide chain begins with analysis and understanding. When a enterprise understands its publicity factors, it may handle them. Whether or not that’s sudden tariffs on supplies or provider delays, dozens of things affect when and the way merchandise attain shoppers.
Listed below are among the main classes of potential delays. Use these provide chain threat examples to search out the vulnerabilities that may affect your operation:
1. Pure and International Occasions
Excessive climate occasions, pandemics, and geopolitical battle all have vital ripple results. They usually occur with little warning and result in long-lasting manufacturing, logistics, and sourcing delays. For instance, when the Ever Given container ship blocked the Suez Canal in 2021, it delayed $9.6 billion price of products per day. It took six days to clear the canal, impacted delivery schedules globally, and precipitated disruptions within the delivery trade.
Commerce wars, sanctions, pandemics, and main disasters have comparable results on the availability chain. Corporations caught in these occasions should have the ability to supply from unaffected areas to take care of manufacturing. If items turn out to be too costly on account of tariffs or sourcing points, your organization wants an alternate technique constructed on world provide chain threat administration.
2. Provider Dangers
Even should you construct up your logistical defenses in opposition to points, there are different vulnerability factors. Weak hyperlinks within the provide chain can shut the whole lot down. Hazards like provider chapter, capability shortfalls, supply delays, and high quality management failures are all potential. When you depend upon just one provider for essential elements, any issues on their finish imply cascading failures.
Operational vulnerabilities additionally pop up round outdated or poor infrastructure. When you lack real-time visibility into stock, how are you going to handle efficiency throughout disruptions? When you lack accuracy when monitoring uncooked supplies, how will you recognize what you’re working out of? Your corporation must have up to date applied sciences and diversified suppliers to scale back the probabilities of dangers halting an operation.
3. Cybersecurity and Know-how Gaps
Digital instruments are a central a part of right this moment’s world. Whereas they make exchanging and managing info simpler, in addition they introduce new dangers. When you depend on cloud techniques and related gadgets, you want sturdy safety in opposition to attackers.

Cyberattacks can cease manufacturing, corrupt knowledge, and expose delicate info. In 2024, the worldwide common price of a knowledge breach was $4.9 million, up 10% from the earlier 12 months. When risk actors ship phishing emails or malware, and group members entry them, it may price your organization. Only a single level in a system can ripple out, resulting in monetary and reputational loss.
Even unmalicious points like cloud service outages or Web of Issues (IoT) failures can disrupt logistics. When your techniques go down, it’s essential be able to act. Associated issues, like a semiconductor scarcity, can restrict manufacturing or stop you from accessing the instruments it’s essential sustain with the competitors.
4. Reputational Dangers
International warming is a priority for shoppers and governments in all places. Trendy provide chains face scrutiny for his or her affect on the setting and human rights. When surveyed, 60% of individuals stated they’d pay extra for sustainable product packaging. Failing to vet suppliers for environmental and social compliance can result in reputational harm or regulatory issues.
Even when your organization strives to remain inexperienced and shield employees at totally different amenities, sourcing uncooked supplies from areas with extra relaxed requirements can have an effect on shoppers. They won’t buy from you on account of these issues. Moreover, firms face stress to restrict their emissions and cut back waste. Overlooking environmental laws can put your online business in danger.
5. Demand Volatility
Shopper conduct now shifts with the newest on-line tendencies, financial issues, and know-how. Many provide chains that function on just-in-time (JIT) fashions can battle to maintain up with these speedy adjustments. For instance, the early COVID-19 pandemic noticed shortages of important objects like rest room paper and canned items. Corporations that lacked a listing buffer struggled to maintain up with demand.
An efficient SCRM technique considers demand fluctuations with predictive analytics, strategic inventory ranges, and versatile scaling.
Why Conventional SCRM Falls Quick and How Danger-Primarily based Approaches Can Assist
Conventional SCRM is commonly reactive and disconnected from totally different firm areas. These strategies take a look at remoted ache factors as a substitute of contemplating how they have an effect on the whole operation. Addressing delays, stock bottlenecks, or single provider points after they happen leaves you in your again foot. They’re momentary options that fail to guard you for the following time one thing occurs.

Two widespread limitations of conventional SCRM are a scarcity of cross-coordination and poor real-time visibility. Danger administration usually sees minimal integration throughout departments. Your IT, compliance, and finance groups might need blind spots or redundant measures since they by no means coordinate. Restricted real-time visibility additionally prevents groups from monitoring vulnerabilities as they modify. With a siloed, digitized provide chain, your operation might need slower response occasions and extra harm. Everybody should work collectively to be proactive to succeed.
What Is a Danger-Primarily based Method?
A risk-based method to SCRM is proactive as a substitute of reactive. You begin by figuring out essential dangers throughout your provide chain. Then, companies anticipate doubtless points attributable to these hazards. You’ll assess how doubtless they’re and what the affect shall be, after which develop controls for limiting them. A centralized enterprise threat administration (ERM) platform could make this course of simpler, making a coordinated, easy-to-navigate area to your SCRM.
What Ought to Your Provide Chain Danger Administration Framework Look Like?
A profitable SCRM program is constructed to be structured, repeatable, and data-focused. Irrespective of your trade or firm measurement, you need to use a robust SCRM framework to scale back vulnerability publicity and hold your online business working. Use this framework as a basis to your firm and create a technique that prepares you for main dangers:
1. Determine

Step one in constructing an efficient SCRM technique is figuring out potential provide chain disruptions. Transcend direct relationships and think about how occasions throughout the whole ecosystem may trigger delays. Contemplate:
- First-tier suppliers
- Third-party dependencies
- Manufacturing websites
- Transportation routes
- Geographic areas with common large-scale occasions
- Important service suppliers
Dangers can be inner, like reliance on a single vendor, or exterior, like extreme climate patterns close to a provider. You want visibility into these dangers to mitigate them. Use sources like an ERM platform with prebuilt threat libraries to search out widespread hazards throughout the trade, provide chain tiers, and laws. Groups can use these libraries to make sure they discover all threat classes.
Map vulnerabilities throughout departments and belongings to keep away from silos. You need an interconnected map that gives a whole image of vulnerabilities.
2. Assess
When you’ve recognized the dangers, it’s time to assess their potential affect and probabilities of taking place. A provide chain threat evaluation relies on preferences, however your operation can use knowledgeable assist, threat scoring fashions, warmth maps, and simulations to evaluate your fundamental dangers. You may also search for platforms that present scoring instruments. These provide chain threat evaluation options allow you to outline scoring thresholds and standards, after which assign a rating to every provide threat.
Understanding the largest dangers lets you recognize the place to focus your efforts. Whereas making ready for lower-likelihood disruptions will be difficult, groups can give attention to the highest-chance and highest-impact areas to maximise threat dealing with effectiveness.
3. Mitigate
Subsequent, companies should combine methods to scale back vulnerability publicity and enhance resilience. It’s not sufficient to know what to anticipate — firms want to reduce the harm a threat can do to productiveness. Widespread mitigation measures embrace:
- Provider diversification: Having a number of suppliers avoids anyone changing into a single level of failure.
- Nearshoring: Relocating operations to a better location shortens provide routes and reduces publicity to world occasions.
- Stock buffers: Protecting stock buffers prevents stockouts throughout shock demand fluctuations.
- Up to date know-how: Spend money on provide chain threat administration know-how that improves transparency and automates processes to spice up effectivity and threat administration.
Mitigation goes past operational fixes, too. Your corporation ought to replace insurance policies, coaching packages, and vendor onboarding to make sure everybody understands hazard dealing with efforts. If a vendor is just too relaxed about safety, knowledge might be breached. Everybody must be on the identical web page relating to stopping dangers.
4. Monitor

Dangers are continually altering, which implies vulnerability administration is steady. After you’ve established mitigation efforts, it’s essential monitor them. Ongoing SCRM monitoring tells you ways groups are managing ongoing dangers and retains you up to date on new threats. Look ahead to dangers by:
- Monitoring key efficiency indicators (KPIs) associated to stock turnover and provide chain motion.
- Reviewing vendor efficiency metrics like supply occasions and defect charges.
- Auditing provider compliance with contracts and regulatory tips.
- Watching climate and geopolitical alerts for related areas.
Organizations also needs to schedule common assessments to make sure constant monitoring. Use annual threat audits or quarterly provider evaluations. Standardized monitoring mixed with real-time knowledge will hold you up to date on the whole provide chain.
5. Report
Reporting is the ultimate step in an SCRM framework. Even the most effective threat administration plan can fail if communication is poor. Danger reporting retains board members concerned and ensures stakeholders perceive the present panorama. Use detailed mitigation documentation and high-level summaries to report on mitigation actions, timelines, and accountable events.
Reporting creates clear trails so you’ll be able to observe dangers, division efforts, and audits. Protecting everybody within the loop ensures nothing slips by means of the cracks. Moreover, reporting improves your online business’s transparency. Groups can see how their efforts are making a distinction, and also you shield the corporate from issues over threat dealing with. Vulnerability duty must be shared by everybody at your organization, not simply the availability chain group.
Recognized vs. Unknown Dangers
Even with a strong framework, you continue to have to know tips on how to navigate provide chain dangers. Some are predictable, whereas others will occur with out warning. Constructing a really resilient operation means being ready to handle identified and unknown hazards.
What Are Recognized Dangers?
Recognized dangers are issues companies can establish upfront and consider utilizing knowledge, previous tendencies, or knowledgeable assist. These dangers are recurring or primarily based on predictable situations. A provider working on slim margins could also be a monetary publicity level, whereas a manufacturing facility in a hurricane-prone space will be flagged for pure catastrophe publicity.
Different identified dangers could be:
- Provider chapter.
- Previous report of high quality points.
- Delays on account of seasonal demand spikes.
- Documented noncompliance with regulatory requirements.
These dangers are measurable and visual inside your provide chain or vendor pool. Danger evaluation in provide chain administration includes scoring and classification fashions to rank these hazards. Analyze identified publicity factors utilizing knowledge and take motion by means of sourcing alternate options or stock buffers.
Put together for identified dangers by:
- Utilizing scoring fashions to prioritize threats.
- Sustaining up to date threat registers.
- Implementing, monitoring, and updating threat mitigation plans.

What Are Unknown Dangers?
Unknown dangers are troublesome or unattainable to foretell. These occasions occur when uncommon disruptions, sudden threats, or hidden ripples happen. One thing like a world pandemic doesn’t observe acquainted patterns. It’s unattainable to foretell when these occasions will occur or how lengthy they’ll affect your provide chain. As a result of unknown hazards don’t observe acquainted patterns, they’re more difficult to detect and quantify for threat evaluation measures.
Unknown disruptions embrace:
- Sudden shifts in regulatory insurance policies round materials exports.
- Sudden world conflicts in a key nation.
- Tsunamis or different climate occasions in a essential provider space.
- An unknown or zero-day vulnerability exploited by a cyber attacker.
Whereas unknown dangers are unpredictable, companies can nonetheless put together for his or her results. The purpose is to develop higher responsiveness, agility, and resilience so your group sees much less harm when disruptions occur. You’ll be able to’t predict each state of affairs, however you’ll be able to bounce again sooner every time.
Put together for unknown dangers by:
- Utilizing simulation workouts to check reactions to sudden occasions.
- Constructing sturdy defenses by means of compliance audits and provider vetting.
- Creating contingency plans with provide alternate options and emergency logistics.
- Utilizing analytics to map threat ripples throughout departments and processes.
How Know-how Can Enhance SCRM
International competitors means provide chains transfer sooner and function leaner. Chances are you’ll be competing with companies on the opposite facet of the world whereas delivering to clients in a totally totally different area from your own home base. Organizations can deploy superior know-how to remain forward of the competitors. Trendy SCRM makes use of know-how to detect and reply to vulnerabilities in actual time.

Look to synthetic intelligence (AI), real-time knowledge, automation, and cloud computing to improve your threat administration in provide chain dealing with and keep on the slicing fringe of provide chain safety.
1. Synthetic Intelligence and Machine Studying
AI and machine studying (ML) are the newest applied sciences altering the sport. They’re integral to predictive modeling, serving to companies anticipate dangers earlier than they hit. These instruments analyze huge quantities of information. They take a look at climate patterns, market tendencies, historic knowledge, provider efficiency, and political info to search out patterns and predict future vulnerabilities.
ML algorithms can detect anomalies in vendor supply patterns. Primarily based on the dangers they see, they’ll advocate various delivery routes or sourcing methods. That approach, the group can pivot proactively, saving money and time. When built-in with ERM platforms, ML and AI provide you with insights tailor-made to your online business and primarily based on real-time knowledge.
2. Actual-Time Monitoring and IoT
The IoT describes a community of sensors and know-how that each one join and share knowledge. Trendy delivery containers, fleets, and warehouse gear can all have gadgets that transmit knowledge to digital monitoring techniques. The result’s fixed real-time knowledge on the whole lot from location and motion to temperature, humidity, and stress.
These real-time monitoring capabilities give firms perception into product standing at each stage. Sensors alert groups to temperature points with delicate items, whereas managers can see stockouts earlier than they occur. The IoT additionally makes delay or recall traceability simpler. Groups can shortly doc, observe, and mitigate publicity as quickly because the IoT alerts them to issues, making response occasions sooner and extra proactive.
3. Automation
Automation is one other software that improves provide chain resiliency. Your corporation can cut back human error and enhance velocity with robotics and automatic instruments. With automated rote work, your operation can transfer by means of manufacturing sooner, with fewer errors in hazardous areas. Search for these automated applied sciences to spice up productiveness:
- Automated platforms: Assess vendor threat scores and flag anomalies with out guide overview.
- Robotic course of automation (RPA): Type, label, and transfer items in warehouses.
- Automated workflows: Analyze knowledge routinely and escalate to human group members if the system detects new threat elements.
4. Cloud Computing
Cloud-based infrastructure is one other strategy to streamline your SCRM course of. Counting on native servers includes investing in your individual on-site knowledge storage, processing energy, and group members to watch and repair points. Cloud computing helps you to share knowledge, develop storage and collaborate with out overextending enterprise infrastructure. Off-site knowledge storage and cloud companies preserve collaboration with stakeholders, regardless of their location.
Use cloud companies to view dashboards, replace threat assessments, and consider provider statuses from any system — even while you’re on the street. Cloud platforms are additionally scalable. Corporations can simply develop their SCRM program as provide chains develop. Plus, cloud-based infrastructure handles updates and safety patches centrally. Everybody will get up to date collectively, avoiding outdated software program and unprotected endpoints.
5. Blockchain Know-how
Blockchain is a clear, unchangeable ledger used to trace transactions and belongings. It may possibly assist higher traceability and anticounterfeiting efforts. When built-in, every transaction or items motion is recorded within the blockchain. It’s a everlasting report of who dealt with what, the place, and when. Blockchain has the potential to assist the availability chain turn out to be extra reliable.
Nevertheless, blockchain know-how is presently troublesome to scale and requires excessive vitality consumption. As a more recent know-how, it has a extra restricted employee pool and has not been extensively adopted. Sooner or later, a extra energy-efficient blockchain ledger may assist handle hazards.
Greatest Practices for Constructing Provide Chain Resilience
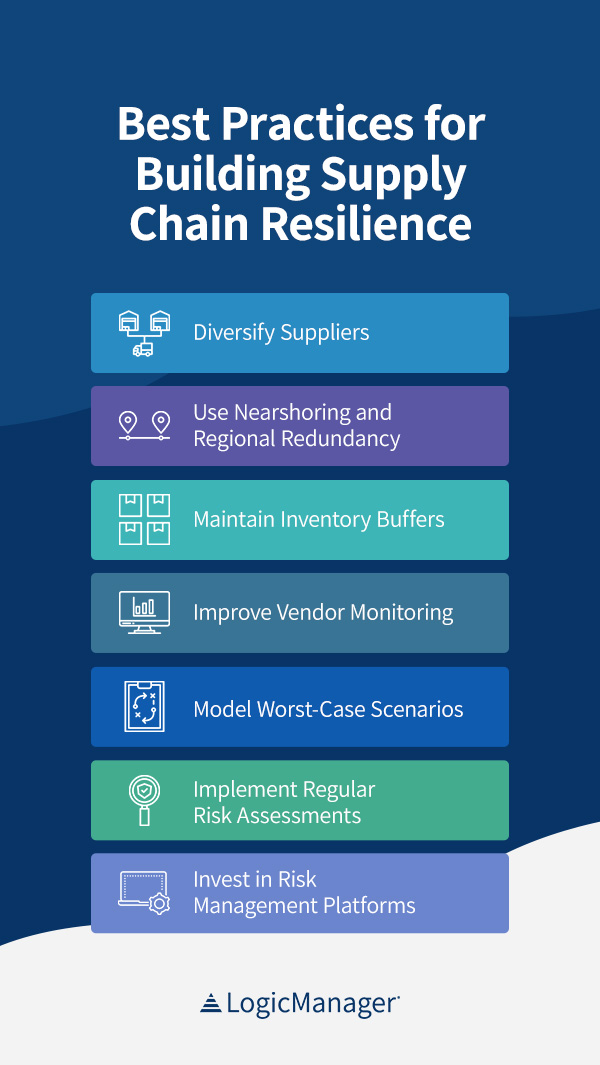
Each enterprise faces a disruption in some unspecified time in the future. Our provide chains are too interconnected to stay unaffected by all dangers. Constructing a resilient provide chain means anticipating challenges and minimizing vulnerabilities. When you’ll be able to put together successfully and reply shortly, you shield the corporate from the worst results of a disruption. Use these SCRM greatest practices to strengthen your provide chain in an ever-changing world:
1. Diversify Suppliers
Counting on a single provider or a small vendor pool for essential supplies and companies is dangerous. If one thing delays their work, you threat a whole shutdown on the first signal of disruption. Diversification spreads your sourcing throughout a number of distributors and areas to mitigate this vulnerability.
Have alternate suppliers recognized and able to go in case of disruptions. Search for distributors in several areas with distinctive logistical paths. If you choose distributors internationally however all of them collide at a particular transport level, that’s nonetheless a serious threat ready to occur. Monitor suppliers, routes, and threat elements from a centralized system and make sure you’re diversified sufficient to scale back disruptions like climate and shock laws.
2. Use Nearshoring and Regional Redundancy
Globalization and outsourcing have allowed firms to deliver down prices. Sourcing from cheaper labor or materials areas maximizes earnings however places you at better logistical threat. The additional away all of your suppliers are, the extra world liabilities you tackle. When excessive climate, political points, and delivery delays sluggish abroad provide, you would face weeks of downtime.
Combine some nearshore or regional redundancy choices to restrict threat impacts. You need to have the ability to supply from teams nearer to your major markets if dangers pop up all over the world. Nearshoring shortens lead occasions and retains you from being too depending on high-risk areas. For instance, investing in sourcing in Mexico or the Midwest for U.S. companies could increase some manufacturing prices, but it surely avoids monetary hits from abroad bottlenecks.
3. Keep Stock Buffers
JIT stock permits firms to scale back warehousing prices, however this leaner operation model additionally exposes them to extra hazards. With sudden demand surprises and world disruptions, JIT stocking leaves you with no wiggle room. Constructing stock buffers for probably the most essential merchandise retains you from coping with stockouts throughout lean occasions.
A tailor-made security inventory bridges the hole throughout disruptions. Even when your suppliers are delayed, you continue to have stock to promote. You’ll make a revenue as you begin up alternate sourcing or logistics plans. A top quality ERM platform will allow you to align stock methods with provide chain threat profiles. The result’s exact security stocking primarily based on real-world knowledge.
4. Enhance Vendor Monitoring

Provider threat is likely one of the fundamental issues when evaluating provide chain liabilities. Your operation wants full perception into third-party efficiency and compliance to make sure there are not any hidden surprises. Make certain to investigate:
- Labor and environmental practices.
- Vendor credit score well being and financials.
- Fourth-party dependencies.
- Cybersecurity controls and knowledge dealing with.
It’s widespread to deep-dive into distributors throughout onboarding. When you’ve accredited a vendor, it’s simple to calm down your oversight and turn out to be complacent. However suppliers can change over time, exposing you to new dangers. Ongoing monitoring is essential for shielding a provide chain. Use common evaluations, audits, and efficiency monitoring to make sure distributors are staying on prime of high quality and safety.
5. Mannequin Worst-Case Situations
Some hazards will hit out of nowhere. Your greatest method is to organize for the most probably and most damaging eventualities so that you’re prepared to reply to the worst disruptions with out problem. Modeling is a good way to coach your online business response and see the affect of particular dangers. Use enterprise affect analyses, tabletop workouts, and simulation instruments to rehearse responses recurrently.
State of affairs modeling exhibits firms the gaps of their communication, useful resource use, and protocols. Proactive testing helps you fine-tune mitigation plans, making them sooner and more practical. Moreover, groups will clear up confusion earlier than the precise occasion, making a more practical response plan.
6. Implement Common Danger Assessments

Dangers are all the time altering. Political instability in a single space could improve abruptly, whereas different areas may see adjustments in climate patterns that have an effect on logistics. Jurisdictions would possibly change their regulatory necessities, affecting markets. With so many variables altering, it’s essential prioritize common publicity assessments in your provide chain threat administration methods.
Inside or exterior elements can affect a provider’s threat ranking. Common assessments ought to consider:
- Publicity to environmental, cyber, or political dangers.
- A provider’s significance to your online business.
- Shifts in compliance or output efficiency.
- Modifications in monetary well being or working situations.
7. Spend money on Danger Administration Platforms
Centralizing your SCRM plan with Software program-as-a-Service (SaaS) platforms can enhance consistency and scalability. Managing vendor knowledge and threat scores from separate techniques results in knowledge silos and redundancies, whereas a centralized system brings the whole lot collectively in a single place.
Use a SaaS-based software that provides real-time dashboards, useful insights, workflow automation, and cross-functional collaboration. You’ll simply juggle complicated knowledge whereas slicing proper to the knowledge you want. These platforms may also combine with third-party instruments so you’ll be able to preserve your operational effectivity. Danger administration platforms provide help to keep forward of latest dangers so your online business can sustain with the competitors.
How LogicManager Helps Smarter SCRM
Even the most effective technique wants supporting provide chain threat administration instruments. Juggling spreadsheets, vendor evaluations, climate knowledge, and all the opposite essential info is a gigantic quantity of labor to your firm. A platform constructed for ERM can assist you keep related and on prime of the newest issues. That’s the place LogicManager is available in.
LogicManager’s ERM platform gives the inspiration a enterprise must design, execute, and scale a wiser SCRM program. Our resolution aligns your provide chain oversight with areas like IT hazards, regulatory compliance, and cybersecurity. With the whole lot in a single centralized place, you get sooner threat administration and fewer silos.

LogicManager’s vary of options makes supporting and scaling your provide chain threat administration options simpler. We provide:
- Prebuilt threat libraries: Our prebuilt threat libraries, controls, and evaluation templates allow you to begin constructing a threat program instantly. These configurable libraries enable firms to tailor their setup to distributors, areas, and compliance necessities.
- No-code implementation: We provide drag-and-drop instruments for simpler legal responsibility evaluation constructing. Create workflows, dashboards, and reviews for your online business’s wants with no developer. This flexibility empowers departments to contribute with out relying solely on IT groups.
- Professional assist: We pair each buyer with a devoted advisory analyst. These vulnerability specialists assist configure workflows, interpret threat knowledge, and supply tailor-made assist. We wish to assist your threat capabilities develop successfully throughout the firm.
- Seamless integration: LogicManager integrates with over 50 third-party techniques, together with BitSight, RiskRecon, DocuSign, Workday, and Workplace 365. You rise up and working sooner and obtain higher collaboration throughout your techniques.
Danger Ripple Analytics
What really units our companies aside is Danger Ripple Analytics. This proprietary software lets organizations visualize how a single disruption can ripple by means of interconnected sectors. A provider outage or contract breach can abruptly turn out to be a listing scarcity, risking productiveness. A compliance problem would possibly affect authorized departments, delay manufacturing, and harm buyer relationships.
By mapping dependencies, LogicManager permits groups to evaluate the total scope and affect of each threat. With detailed Danger Ripple Analytics, you’ll be able to construct extra responsive, particular mitigation methods. Our resolution offers you a full view of your vulnerabilities and the way they may have an effect on operational success.
SCRM Regularly Requested Questions
Whether or not you’re constructing an SCRM framework from the bottom up or refining your present plan, understanding the fundamentals of provide chain hazards is important. Listed below are some solutions to widespread questions that will help you higher consider your dangers and mitigation efforts.
1. What Are the 4 Kinds of Danger in Provide Chain Administration?
The 4 fundamental sorts of dangers in provide chain administration are political, financial, environmental, and moral. Most dangers fall into a number of of those classes. Your corporation and its suppliers, distributors, and companions are all affected by one in all these dangers in some unspecified time in the future. International SCRM methods think about these classes and rank the largest issues to scale back their affect after they occur.
2. What Are the High Provide Chain Dangers?

Dangers are continually altering, and totally different teams will consider them in another way. A number of the prime provide chain dangers in 2025 are:
- Local weather change
- Geopolitical instability
- Rising cybercrime
- Mineral shortage
- Pressured labor issues
3. What Are the SCRM Reliability Requirements?
The SCRM Reliability Requirements are tips to assist excessive and medium affect bulk electrical system (BES) Cyber Methods deal with dangers. They lay out safety goals for these companies to allow them to mitigate vulnerabilities. Whereas they apply to BES Cyber Methods, noncyber firms can use them to refine their SCRM method.
4. How Does SCRM Relate to ERM?
Enterprise threat administration is a framework for managing issues throughout a complete enterprise. SCRM focuses in your provide chain particularly, equivalent to provider relationships and logistics. ERM platforms join your SCRM knowledge to different areas like IT, finance, and compliance. This fashion, you get the entire threat image and see how each space impacts the others.
5. What Is the Distinction Between SCRM Software program and Provide Chain Administration Software program?
Provide chain threat administration software program streamlines managing and decreasing provide chain dangers, significantly third-party, operational, cybersecurity, and compliance liabilities. Provide chain administration (SCM) software program is constructed for overseeing logistics, procurement, transportation, and stock. Danger administration in SCM is essential for shielding enterprise operations.
6. How Do You Consider Danger Administration Instruments?
Discovering the precise ERM platform to your SCRM technique is essential. Search for:
- Customizable threat evaluation templates
- Third-party integrations
- Centralized dashboards and threat registers
- Cross-functional collaboration
- State of affairs modeling instruments
- Workflow automation
- Professional assist for troubleshooting and technique
Take Management of Your Provide Chain Dangers With LogicManager’s Options
Your SCRM program must be proactive and reactive. Companies should keep on prime of real-time knowledge, altering dangers, and world occasions to maintain their provide chains shifting. LogicManager empowers organizations to attach provide chain oversight with enterprise-wide threat administration. Our unified, risk-based method lets all operations discover and mitigate dangers for higher enterprise continuity.
You get full visibility throughout all departments with LogicManager’s Danger Ripple Analytics, ERM resolution, and knowledgeable advisory companies. From day-one onboarding to outcome-driven licensing and stuck pricing, we simplify scaling your SCRM program with out added complexity. Allow us to provide help to construct a extra environment friendly, efficient provide chain. Get began along with your free demo right this moment.


