As third-party associated points and breaches develop extra frequent and dear, their total affect on enterprise operations and model belief has turn out to be inconceivable to disregard. An alarming statistic within the Verizon 2025 Knowledge Breach Investigations Report highlighted that 30% of knowledge breaches concerned a 3rd celebration, up 15% from the earlier 12 months, making third-party threat administration a prime concern for CISOs.
RSAC ESAF CISOs Reworking Third-Occasion Danger Administration
Though the trendy know-how provided by third-party distributors gives companies with a wealth of capabilities to streamline and automate processes, every vendor turns into a brand new assault vector and exposes companies to new dangers.
Vendor know-how points typically result in operational failures, system downtime, compliance violations, knowledge breaches, and reputational harm, impacting model belief. In a bid to exhibit resilience to the board, CISOs understand they’ll not handle third-party threat in isolation. As an alternative, they have to handle it proactively, integrating it into their broader cybersecurity, GRC, and organizational resilience technique.
Third-party distributors are an integral a part of a corporation’s ecosystem, and any failure may cause catastrophic penalties. As distributors turn out to be a part of the prolonged enterprise, companies anticipate them to uphold the identical requirements in enterprise continuity planning, regulatory compliance, certifications, incident response, and threat administration. Subsequently, it’s simple to see why organizations more and more view third-party threat administration not as an remoted self-discipline however as an extension of their present processes.
When achieved nicely, third-party threat administration can be utilized as a strategic benefit to empower organizations to embrace new know-how and smarter working strategies. Modern CISOs can harness third-party threat administration and use it as an enabler to maneuver quick with AI, cloud know-how options, and third-party integrations. Slightly than blocking innovation to keep away from threat, sturdy vendor threat practices ought to empower you to confidently interact promising new companions, with the correct onboarding, expectations, and controls in place.
Latest Studies Spotlight Third-Occasion Danger as an Enterprise-Extensive Concern
With such widespread use of third-party applied sciences, one may assume organizations would prioritize managing their related dangers. However, within the newest Forrester report, The State of Third-Occasion Danger Administration, 2024, solely 8% of worldwide threat administration decision-makers chosen third-party threat of their prime 5 enterprise threat administration issues.
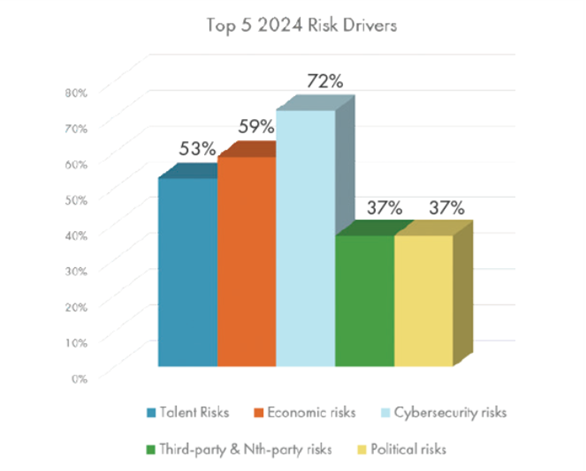
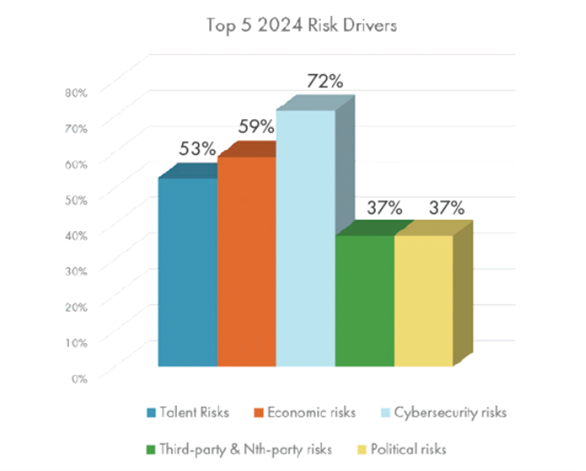
At first look, the outcomes recommend that organizations give restricted consideration to third-party threat. Nevertheless, a better look reveals that the highest dangers recognized by threat leaders—similar to knowledge privateness, data safety, rising know-how, regulatory compliance, enterprise continuity, operational threat, and provide chain threat—are all inherently linked to third-party relationships. Subsequently, quite than viewing third-party threat as a standalone class, the survey outcomes recommend organizations acknowledge that third-party threat administration have to be embedded throughout their broader enterprise threat panorama and managed holistically. The latest leads to The 2024 New Technology of Danger Report by Riskonnect discovered that 72% of firms surveyed thought of cybersecurity to be a prime threat driver in 2024, whereas 37% cited third-party and Nth celebration dangers as a prime precedence, additional highlighting the shut hyperlinks between third-party threat and cybersecurity.
Regulatory Strain Brings an Elevated Deal with Third-Occasion Danger Administration
Third-party threat reliance is rising, and laws are accelerating consistent with this pattern. With so many know-how distributors flooding the market and AI options booming, it’s no shock that many broadly adopted laws contact on managing the dangers related to service suppliers. ISO 27001, NIST, NIS2, COBIT, HIPAA, DORA, SEC, the GDPR, and APRA CPS 230 all embody steerage on managing third-party threat. Complying with laws calls for visibility and management, and a well-established third-party threat administration program helps companies in demonstrating that their vendor community aligns with regulatory necessities.
CISO Accountability for Vendor-Associated Incidents is Rising
As third-party threat administration packages have matured, organizations more and more maintain the CISO—not the contracting division—accountable for vendor-related incidents. This elevated stress and accountability have seen third-party threat administration packages mature quickly as CISOs implement further checks and measures to safeguard the corporate and its status.
Right here Are 6 Methods Proactive CISOs Flip Third-Occasion Danger Administration right into a Strategic Benefit
1. Tie Vendor Danger to Enterprise Continuity and Incident Response Plans
Proactive CISOs perceive {that a} breach, outage, or failure by a crucial vendor can grind operations to a halt. Slightly than treating vendor threat as a separate concern, sensible CISOs combine it straight into enterprise continuity planning (BCP) and incident response playbooks. This strategy helps make sure the group can proceed working throughout a vendor disruption—whether or not attributable to cyberattacks, compliance failures, or operational breakdowns—and protects what issues most: avoiding pricey enterprise disruption and preserving model belief. These outcomes resonate on the board degree and assist CISOs body third-party threat as a core element of total cyber resilience.
To combine these processes efficiently, your third-party threat administration program should:
- Map vendor providers to business-critical capabilities
- Determine which third events underpin core techniques, processes, and regulatory obligations
This mapping lets you perceive the potential affect if a crucial vendor fails and permits for risk-based prioritization of distributors in continuity planning.
As well as, organizations must also:
- Plan situation and vulnerability testing workout routines that embody third-party failures to make sure preparedness extends to crucial third-party distributors.
- Set up backup distributors and contingency plans.
- Guarantee vendor assessments enquire about enterprise continuity plans, incident response processes, and restoration time aims to make sure their inner processes align with organizational expectations.
Because the variety of third-party distributors will increase, so does the probability of vendor-related incidents and disruptions. To make sure well timed and efficient decision, organizations should set up a clearly outlined incident reporting course of that captures third-party-related incidents, hazards, and close to misses. These plans ought to embody escalation protocols, communication plans, and remediation procedures.
2. Use Vendor Due Diligence to Drive Innovation and Digital Technique
Whether or not it’s AI, new markets, or digital rollouts, daring CISOs deal with third-party threat as an enter to innovation, quite than viewing it as an impediment. Within the Forrester report cited earlier, knowledge exhibits that respondents who made the connection between elevated ranges of enterprise threat and elevated reliance on third events ceaselessly describe threat administration as an accelerator of innovation.
Sturdy third-party threat administration permits CISOs to conduct due diligence shortly and confidently, permitting them to approve high-impact vendor partnerships with out compromising safety or compliance. This assurance is crucial when adopting cutting-edge platforms or AI-powered instruments.
To make quick, assured selections, efficient TPRM packages give attention to a couple of crucial actions:
- Performing fast threat assessments tailor-made to the seller’s position and threat profile
- Leveraging AI and threat intelligence to flag points referring to monetary stability, compliance, or cybersecurity
- Making certain clear expectations round SLAs, KPIs, and incident response
This strategic strategy ensures that modern distributors—particularly smaller or extra agile suppliers—will be onboarded immediately, guaranteeing they meet your thresholds for resilience and alignment with regulatory requirements.
By embedding these controls early within the choice course of, CISOs can transfer shortly with out compromising the group’s threat urge for food. Third-party threat administration permits digital progress, empowering innovation groups to maneuver quicker with confidence.
3. Elevate Third-Occasion Danger to Present Board-Stage Visibility
CISOs ought to elevate third-party threat to the boardroom by framing it when it comes to operational resilience, reputational threat, regulatory publicity, and monetary penalties. CISOs who articulate vendor threat by highlighting enterprise affect and long-term resilience get buy-in quicker and safeguard belief with government groups. There’s additionally a threat in standing nonetheless. Boards should perceive that avoiding new know-how can create as a lot publicity as adopting it. This translation of threat knowledge into significant metrics is important for getting buy-in for brand new strategic distributors and gaining government help for stronger third-party threat administration packages, ongoing funding, and cross-functional engagement.
When achieved nicely, third-party threat administration turns into a strong management device that helps CISOs transfer shortly and get approvals to implement new know-how, enabling their organizations to remain forward of the curve in an more and more aggressive market. CISOs who recurrently increase vendor threat in board conferences and current significant metrics usually tend to safe sources and affect vendor choice selections, serving to their firms undertake new digital options that advance the enterprise mannequin.
Board-level visibility of third and fourth-party dangers limits surprises when incidents happen. Profitable third-party threat administration packages guarantee management groups are already aligned on response protocols, escalation procedures, and the potential affect of a failed vendor, minimizing panic when vendor-related incidents do happen.
4. Join the Dots Throughout Groups and Instruments
Much less mature organizations typically retailer third-party threat knowledge throughout disparate techniques and knowledge sources. Completely different groups and departments onboard distributors with none central level of oversight, and the vetting course of lacks consistency. In different circumstances, procurement has contracts, IT owns entry administration, compliance tracks certifications, and threat groups handle assessments. In a fragmented surroundings, groups typically miss due diligence steps, overlook crucial warning indicators, and ship disjointed response efforts. Disconnected knowledge and instruments restrict visibility, impairing well timed threat detection. This lack of oversight makes prioritizing mitigation or reporting precisely to the board more durable for CISOs and straight impacts their capability to steer strategically.
Proactive CISOs acknowledge that this strategy lacks consistency and oversight and use third-party oversight to interrupt down partitions. They centralize vendor knowledge in shared platforms or dashboards and implement constant processes for onboarding, conducting threat assessments, benchmarking, scorecarding, and performing due diligence checks to keep away from lacking threat alerts.
This unified strategy ensures a good analysis of distributors by cross-functional governance buildings that automate knowledge sharing between techniques. It provides threat leaders a holistic view of vendor threat and dependencies, empowering them to prioritize mitigating probably the most crucial dangers and maintain the board knowledgeable.
Standardizing your threat framework, evaluation templates, due diligence processes, onboarding, and offboarding makes distributors extra comparable, making it simple to detect poorly performing, high-risk distributors. Entry to interconnected third-party threat administration knowledge permits the board to make quicker, extra knowledgeable selections when selecting new distributors and know-how companions.
In accordance with OCEG, “CISOs are not simply technical specialists. They’re boardroom voices guiding enterprise technique, and the GRC perform is evolving proper together with them”. CISOs should work with GRC groups to harness the proper knowledge to advise the board on the most effective motion to guard the group from cyber and third-party threat.
5. Shift From Static Assessments to Steady Monitoring
The strongest third-party threat administration packages incorporate real-time, steady monitoring of distributors and their efficiency and think about their affect on crucial providers. A latest OCEG article said that “Actual-time threat intelligence is now anticipated. Whether or not it’s steady management monitoring, real-time vendor scoring, or predictive alerts about regulatory adjustments, organizations are anticipated to know that their threat controls are efficient”.
Preliminary assessments throughout onboarding and annual opinions are not adequate to remain forward of third-party dangers. SecurityScorecard’s 2023 breach analysisstates that not less than 29% of all breaches concerned third-party assault vectors. Vendor threat evolves quick, and CISOs want close to real-time visibility and steady monitoring to remain forward of rising threats.
CISOs on the forefront use real-time knowledge to trace adjustments in vendor efficiency. They subscribe to third-party threat intelligence suppliers to grasp if suppliers are hitting the headlines due to monetary instability, compliance violations, and moral mishaps. Additionally they carry out common threat assessments and conduct questionnaires on a month-to-month or quarterly foundation to detect adjustments in circumstances that might pose a threat. Vendor-reliant processes can be factored into common enterprise continuity plan updates and situation and vulnerability testing, guaranteeing enough contingency planning.
This steady monitoring permits organizations to be extra agile and proactive as an alternative of ready for a yearly overview or a disaster earlier than re-evaluating a vendor! With ongoing monitoring, common assessments, and due diligence, CISOs can determine early warning alerts and take preventive motion. This built-in best-practice strategy additionally helps extra correct threat scoring based mostly on how every vendor connects to crucial providers, quite than treating all distributors equally. This ongoing stream of knowledge referring to distributors and their efficiency permits companies to make dynamic, responsive selections on their alternative of distributors and act shortly to avert vendor-related crises.
6. Leverage AI
AI is accelerating quickly, and at present’s CISOs should look past the hype to harness AI’s actual, sensible worth, notably in managing third-party threat. By embedding AI into their processes, CISOs can remove handbook, repetitive duties, floor insights quicker, and reply to rising threats with higher agility. AI is crucial in third-party threat administration, the place manually assessing a whole bunch – and even hundreds – of distributors is not sustainable.
AI can streamline onboarding, automate due diligence checks, flag anomalies in vendor habits, and even predict future threat based mostly on historic patterns and exterior knowledge. It permits CISOs to scale their oversight with out growing headcount and to maneuver from reactive assessments to proactive threat intelligence.
OCEG says, “Generative and agentic AI can already auto-populate threat assessments, detect management redundancies, scan laws, and even summarize weekly threat reviews into government insights. However whereas AI guarantees huge beneficial properties in productiveness, it additionally introduces new dangers: hallucinations, bias, knowledge privateness violations, and unclear possession.”
As a result of AI brings huge alternatives and severe dangers, sensible CISOs ought to lead the dialog, not watch from the sidelines. Those that embrace AI responsibly, with sturdy governance and controls, will place their organizations to mitigate third-party threat extra successfully and acquire a aggressive edge. AI isn’t just one other device, however a strategic benefit for many who use it correctly.
Third-Occasion Danger Administration as a Driver for Strategic Benefit
In an more and more digital and interconnected enterprise panorama, third-party threat administration isn’t just there to stop operational and compliance points; it’s a strategic enterprise enabler. Proactive CISOs acknowledge that third-party distributors broaden the assault floor and handle them with the identical rigor as inner processes. By embedding third-party threat administration and AI into core areas like enterprise continuity, digital transformation, government decision-making, and day by day threat administration actions, CISOs flip vendor threat administration into a significant supply of intelligence that allows their organizations to undertake fashionable know-how at tempo.
Essentially the most forward-thinking CISOs are not content material with reactive or disjointed approaches. They’re shifting towards built-in, strategic provider threat administration packages that scale back threat and unlock alternatives to innovate and develop. The rigorous steady monitoring and vetting in at present’s third-party threat administration packages and the elevated use of AI present very important knowledge to help decision-making, enabling a pre-emptive strategy that addresses vendor threat earlier than it turns into problematic.
Managing third-party threat holistically drives resilience, agility, and long-term aggressive benefit. CISOs should transfer from a mindset of threat avoidance to considered one of assured, risk-informed innovation by utilizing third-party threat knowledge to determine points and dependencies of their vendor ecosystem, guaranteeing their organizations are poised to undertake new know-how and repair suppliers confidently.
Need to go deeper? Discover this e book on third-party threat administration to see how organizations are evolving their packages to fulfill at present’s challenges, or contact Riskonnect for a demo of our third-party threat platform.